Internet Security – Part 1: Who’s responsible?
Security = Trust
Everybody is familiar with exhortations from banks, retailers, social media companies, Internet service providers.. the list goes on … to keep our login credentials (IDs,passwords, PINs) safe and to be sure not to reveal them. When a breach occurs against one of your accounts you can be sure that the first finger of blame gets pointed at you.
- Your debit card was used without your permission? You must have revealed your PIN or security codes to someone else.
- Someone just emptied your bank account using your on-line credentials. It must have been you who let someone gain access to your “keys”.
- Somebody just took over your YouTube account and within seconds Google has emailed half-a-dozen times to tell you that you are posting prohibited material and thirty seconds later that your account has been frozen – and all appeals to have it unfrozen are rejected by autobots – leaving your reputation tarnished, despite the fact you haven’t used your YouTube login in years. Still, it’s your fault. (????)
But– hang on a minute. Security is a mechanism that establishes trust. Trust on the Internet is no different from trust in the real world – it’s a two-way relationship in which both parties have to be trustworthy.
A real world example
Take an example. You have some valuable documents – maybe some photographs as well. You rent a safety deposit box at a bank. Having signed the terms and conditions you are assigned a box, given a key and you store your documents. So, where’s the trust? The bank trusts you to keep your key safe (otherwise you aren’t easily getting your documents back) and you are trusting the bank not to let anyone else – not another customer, not a bank employee, not a robber who walks in off the street to have access to your box or be allowed to copy your documents. In particular, while you know the bank has a master key and other copies of your key you are trusting it to keep those safe and out of other peoples’ hands.
You <==> TRUST <==> Bank <==> TRUSTS <==> You
The Internet reality
So what happens on the Internet? Fundamentally, the relationship should be the same. It doesn’t matter whether you are signing up for on-line banking, an email service, a social media account or some file storage. The service provider is issuing you a key (some credentials) and you are trusting it to keep its keys and the possessions (money or personal data) you give into its care safe and accessible to only you and those you give permission to.
This is where the physical (real) and virtual (on-line) worlds diverge.
The Internet – Who can you trust?
As events over the past few years have shown, the trust placed by users in major Internet service providers is neither respected nor deserved by those providers.
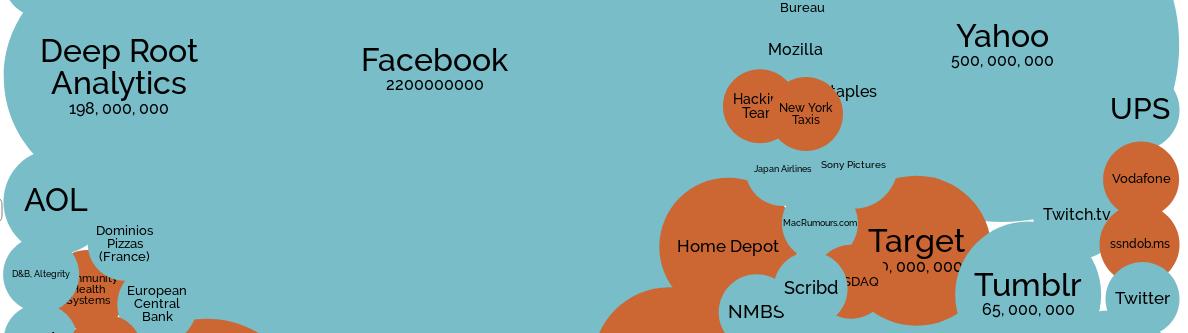
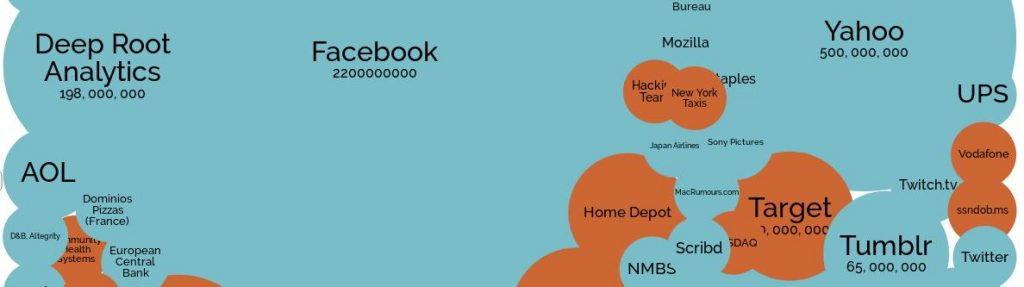
Barely a week goes by without another report of a security breach affecting the users of one of the major Internet service providers –involving at least the loss of those login credentials (your “keys”) and perhaps much more data about you – much of which you may never have known the organisation had on you in the first place.The number of users affected is not small: 3 billion Yahoo users (a fact it saw fit to keep to itself for more than two years), hundreds of millions of customers of Google, Ebay, Yahoo, Facebook, Microsoft… the list goes on. It’s almost unfair to name and shame these companies as they no more deserve singling out than other service providers whose security records are just as inglorious.
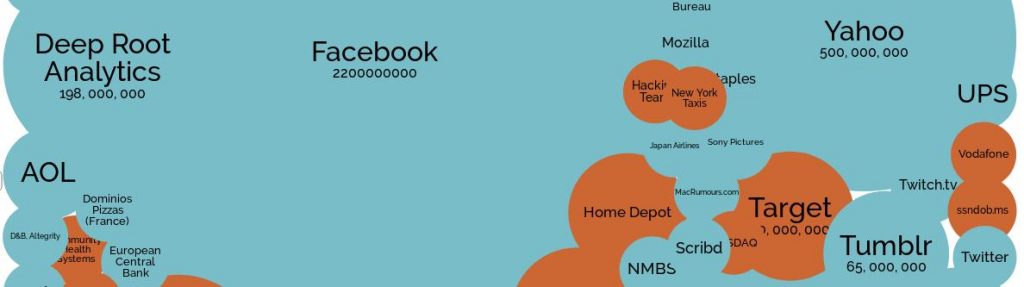
The image above is available in full at informationis beautiful. I encourage everyone to take a look at it to get an idea how big is theproblem of data breach (the loss of your data by companies you trust to keep it safe) – and how it is getting worse over time not better. Disgracefully, the same companies appear time and again – Facebook, Yahoo, AOL (now Oath – new owner of Yahoo), British Airways … Do they not learn the lessons the breaches teach… or do they just not care? The list also contains a number of apps and other services that are actually owned and operated by tech giants such as Google and Facebook – combine them with the parent’s own admitted breaches to get a better understanding of just how sloppy these companies are.
Note that the breaches shown are only those that are known to have occurred. Yahoo failed to disclose the loss of a mere 3 billion customer records for as long as three years before regulations surrounding its enforced sale forced its hand into revealing the information. Many more companies never publish the data they lose – or, disgracefully, ever let the people whose data has been lost know they are now potentially vulnerable to fraud, identity theft or other criminal activity.
In the banking and financial sectors, banks such as America’s largest, JP Morgan Chase, lost confidential information of 76 million customers – that’s half of all households in the U.S.A. to give a little perspective. The credit assessment bureau Equifax (a major personal data aggregator – a tale for another article) went one better by allowing the personal data – including social security numbers, birth dates, addresses, drivers’ licence details and credit card details of 149 million individuals – many of whom have no direct relationship with the company, so hardly gave up their data willingly in the first place – to be exposed. A polite term to describe allowing personal data to fall into the hands of hackers who then happily sell and trade it around in order to conduct financial fraud, identity theft or,as in the Facebook / Cambridge Analytica scandal attempt to sway voting intentions – among other serious crimes.
It’s likely that among the big names on the information is beautiful graphic there are many more organisations you will not recognise – nor have any idea that they may be holding your confidential personal data. Click on “DeepRoot Analytics” to discover that the full name, address, date of birth, race, religion and much more on all 200 million American voters was left out in the open for anyone to take.
“Whoops – sorry!”
In some cases, the mere source of the data also reveals much about the person whose details have been revealed – as users of services like Grindr and Ashley Madison have found to their personal cost.
And, behind the “big name” tech giants everybody recognises, there is an army of supporting companies – providing services such as login security services, payment processing services … and even the company that issues the security certificates used by many of the world’s top commercial web sites to secure the mechanism used to provide supposedly secure shopping, banking and payment systems –the very encryption system used by the web. All have suffered significant data breaches.
The reality is that nobody can be trusted.
That statement is probably worth reading again. NOBODY can be trusted.
The simple fact is that an organisation that has yet to admit having “been hacked” or suffered a security breach (ie; let its customers’ personal data fall into the hand of crooks) is either (in most legislations, illegally) hiding the fact or is merely in line waiting to be hit.
Why is this important?
Beyond the obvious (who actually wants their personal data available to hackers and criminals?) this “lost” data is the basis of spam email, phishing scams, identity theft, fraud and other crimes.
I have first hand experience of the kind of outcome that is possible.On a multi-week driving trip through Europe, on trying to check out of a hotel I found that my credit card was denied. A phone call to the bank revealed that I had recently “changed my address” (to the opposite end of the UK) and had maxed out my spending limit buying building supplies from a firm in Manchester! Reality check: a criminal had combined data from several breached databases to obtain the “security” information demanded by the bank (my date of birth, my mother’s maiden name, my two previous addresses …) – then simply phoned the bank over the space of a few days first to report a change of address, then to request a replacement card “lost in the move” and finally to request a new PIN. In under a week the crook had full control of my account and got busy withdrawing cash and going on a spending spree in my name. I was lucky I could prove I was anywhere but where these fraudulent transactions had taken place – I was busy using my “old” card to pay for fuel, meals and hotel stops across Europe – and had the receipts and photos to prove it. But the cost in time and inconvenience – let alone what would have happened to the rest of my trip or my ability to return home had this been my only means of payment – was considerable.
Other unlucky folks have found debt collectors or court bailiffs at their doors demanding repayment of loans they had never taken out –some crook had used data stolen from voter registration records, the Equifax breach or a hundred other data sources to fill out a form that convinced a loan company to provide the cash to buy a new car/boat/house … leaving the innocent victim to sort out the eventual mess when the loan failed to be repaid.
Others have found that pictures they had (probably unwisely – but that’s another article) uploaded to “secure” file storage sites or to toy and game companies “allowing” children to personalise their on-line account with their photo … suddenly shared all over the web. I imagine that the embarrassment or horror is as nothing to the feeling of betrayal and breach of trust.
So, just who is responsible?
The answer in many cases is that the service provider is responsible for “losing your keys”.
If you are sure that you have not given someone your credit or debit card and PIN – or you haven’t written down your bank login ID and password and stuck the note at the front of your drive or garden for every passing rogue to read – or you haven’t released the details of your YouTube login – and your account gets “hacked” … then be prepared to argue.
Before making a fuss and perhaps ending up with egg on your face, check with a service such as “have I been pwned” (https://haveibeenpwned.com/) which monitors all data breaches and the subsequent data that becomes available from those breaches and allows you to check whether your email address(es) has been exposed in a potentially unrelated breach. Of course, if you are dealing with a service that does not use your email address as part of your login credentials or you (sensibly!) use a separate, random password for each service you log in to then you may choose to skip this step.
Though the law (especially here in Europe) is making it harder and now illegal for companies and organisations to conceal data breaches the majority of past data breaches have gone unreported – and, unless they have already been publicly revealed to be guilty of a security breach, a corporate entity’s first instinct will always be to deny responsibility.
As long as you are sure you haven’t let your login details escape or become known to others do not accept statements that “our systems are secure and infallible” (because they’re not) or accusations that “you must have given someone your details” (because you know you haven’t). Make the company provide details of precisely when and from where (at least the IP address) any disputed access or activity occurred. Use a service such as IP Location (https://www.iplocation.net/) to look up the geographic location of any IP address provided – it goes without saying that if you have never been near the location that is strong evidence that you did not perform the disputed act. Also make the company provide all the data they have on the disputed activities. If you (or they) are in Europe then the EU-wide GDPR legislation applies – and they cannot argue both ways … GDPR requires an organisation to hand over a copy of ALL data it holds on you – which includes disputed transactions, login logs etc., etc. The organisation cannot argue that you are responsible for an action and then refuse to hand over data which, by their own description and claim, is yours.
Essentially, make the company prove you responsible. Don’t accept that you have to prove your innocence (if necessary, remind them that proving a negative is impossible) but make them do the running to concretely prove your responsibility.